Vulnerability Management Platform
Everything Your Security Team Needs to
Find, Track, and Fix Vulnerabilities
From reconnaissance to final report — Hawkra unifies vulnerability management, penetration testing workflows, and compliance for security teams and solo operators alike. Cloud or self-hosted.
Import from Nmap, Nessus, OpenVAS, Burp, ZAP, BloodHound & more
Every credential, note, and file encrypted with per-workspace keys
NIST CSF 2.0, ISO 27001, and CIS Benchmarks with auto-populate
A Complete Platform for Security Teams
Every tool your team needs to manage vulnerabilities, from initial reconnaissance through remediation and compliance reporting.
Vulnerability Tracking
Track vulnerabilities across your entire attack surface with CVSS scoring, CVE/CWE mapping, and multi-status workflows from discovery to remediation.
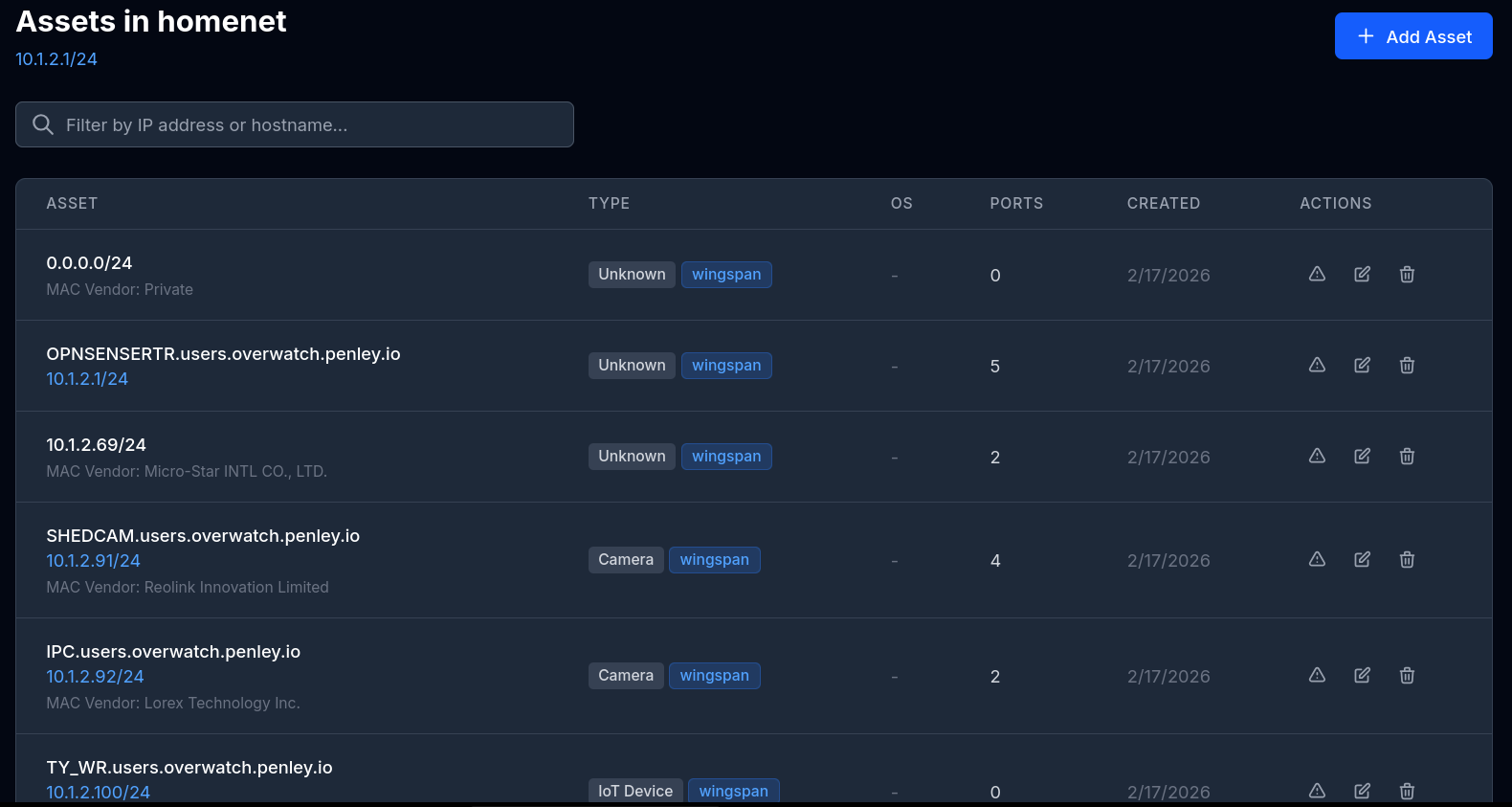
Asset & Network Management
Organize your infrastructure with network scoping, 15+ asset types, port and service discovery, OS detection, and MAC vendor classification.
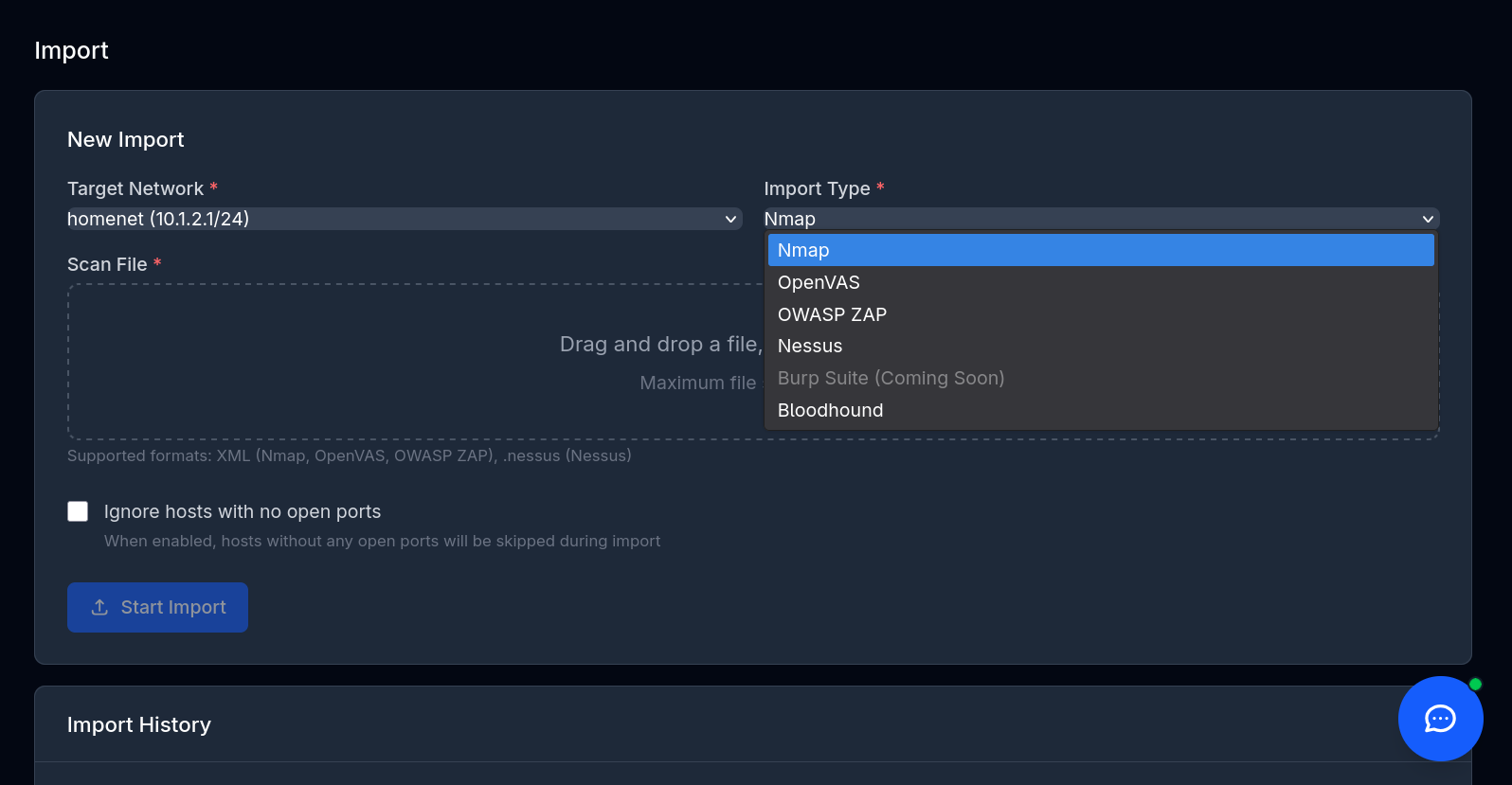
Scanning & Imports
Import results from 7 scanner formats or deploy WingSpan, our integrated scanning agent, to scan remote networks. Auto-create assets and vulnerabilities from scan data.
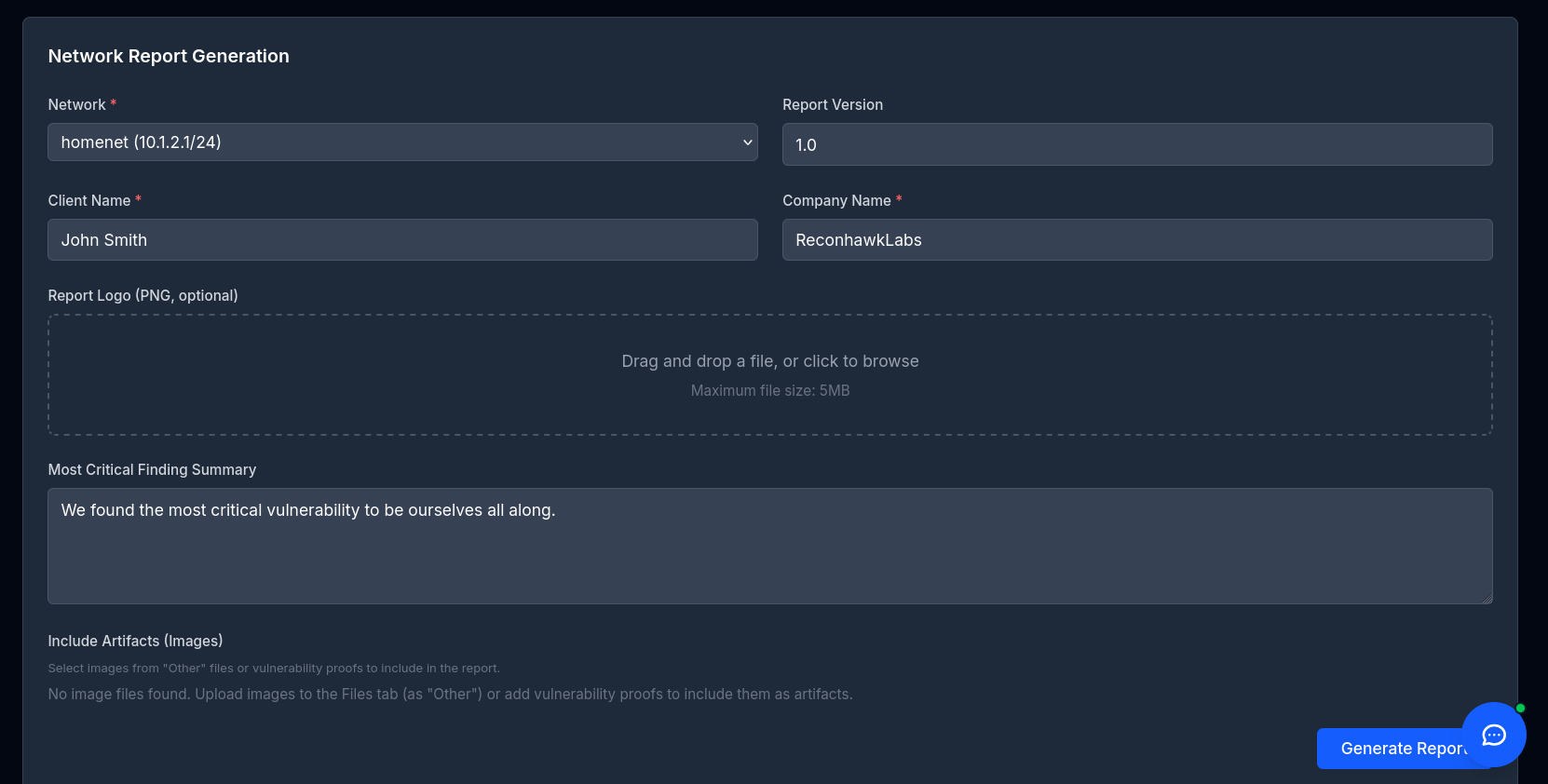
Professional Reporting
Generate client-ready DOCX reports with customizable templates, risk scoring, and embedded evidence.
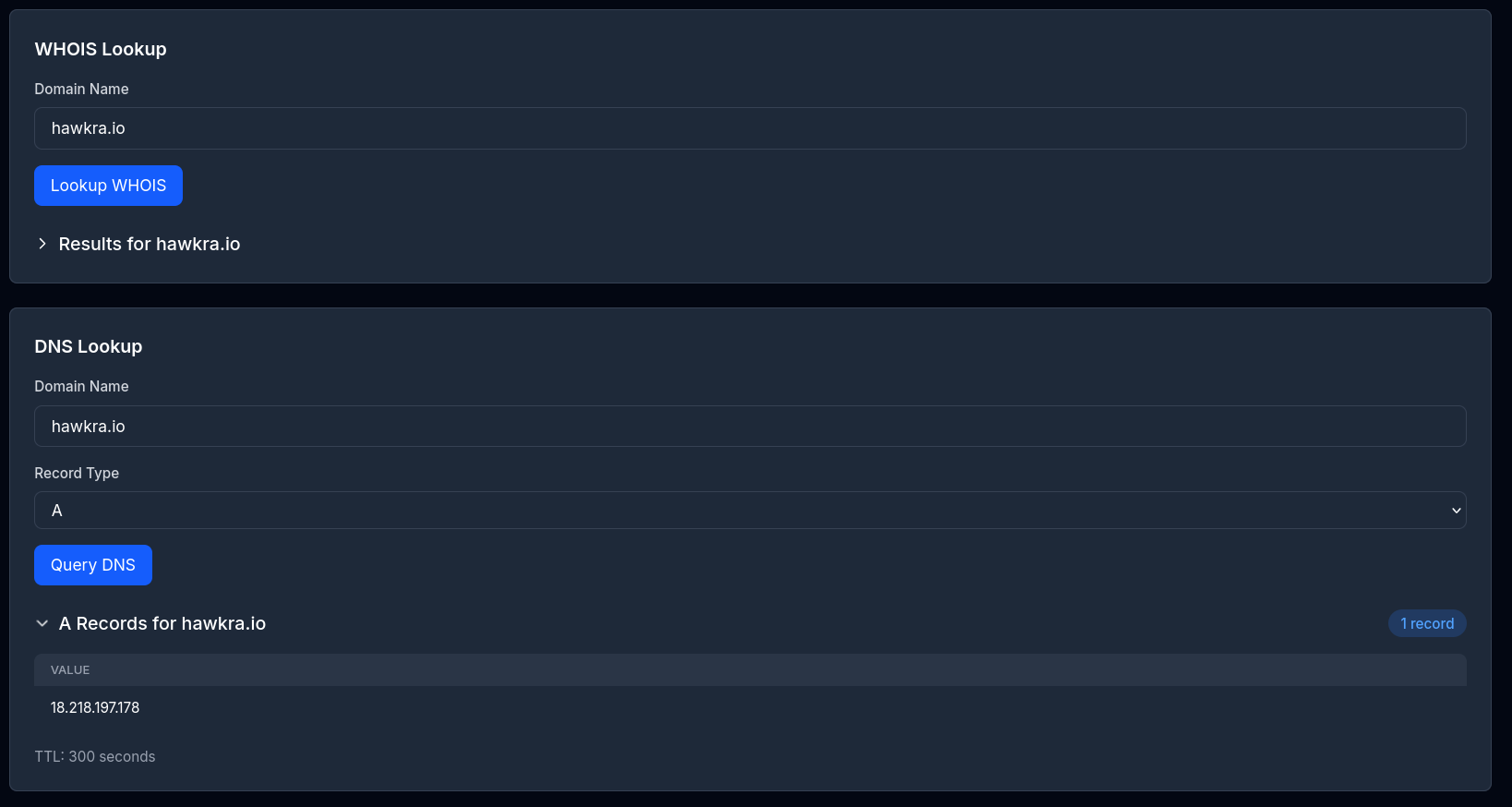
OSINT & Reconnaissance
Built-in WHOIS, DNS, Shodan, Have I Been Pwned, and GeoIP lookups — all without leaving the platform.
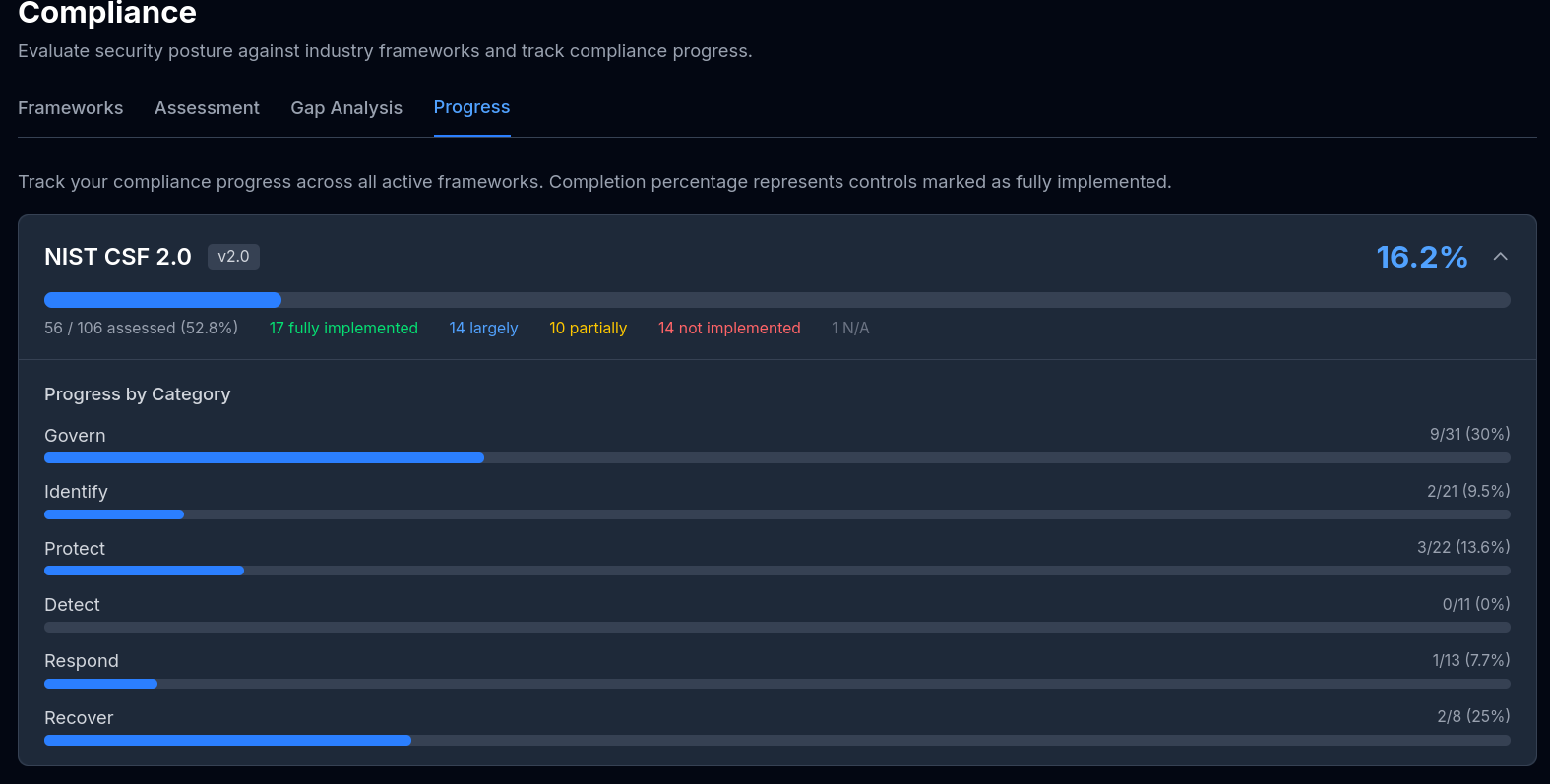
Compliance & Auditing
Assess against NIST CSF 2.0, ISO 27001, and CIS Benchmarks. Auto-populate controls from scan data with gap analysis.
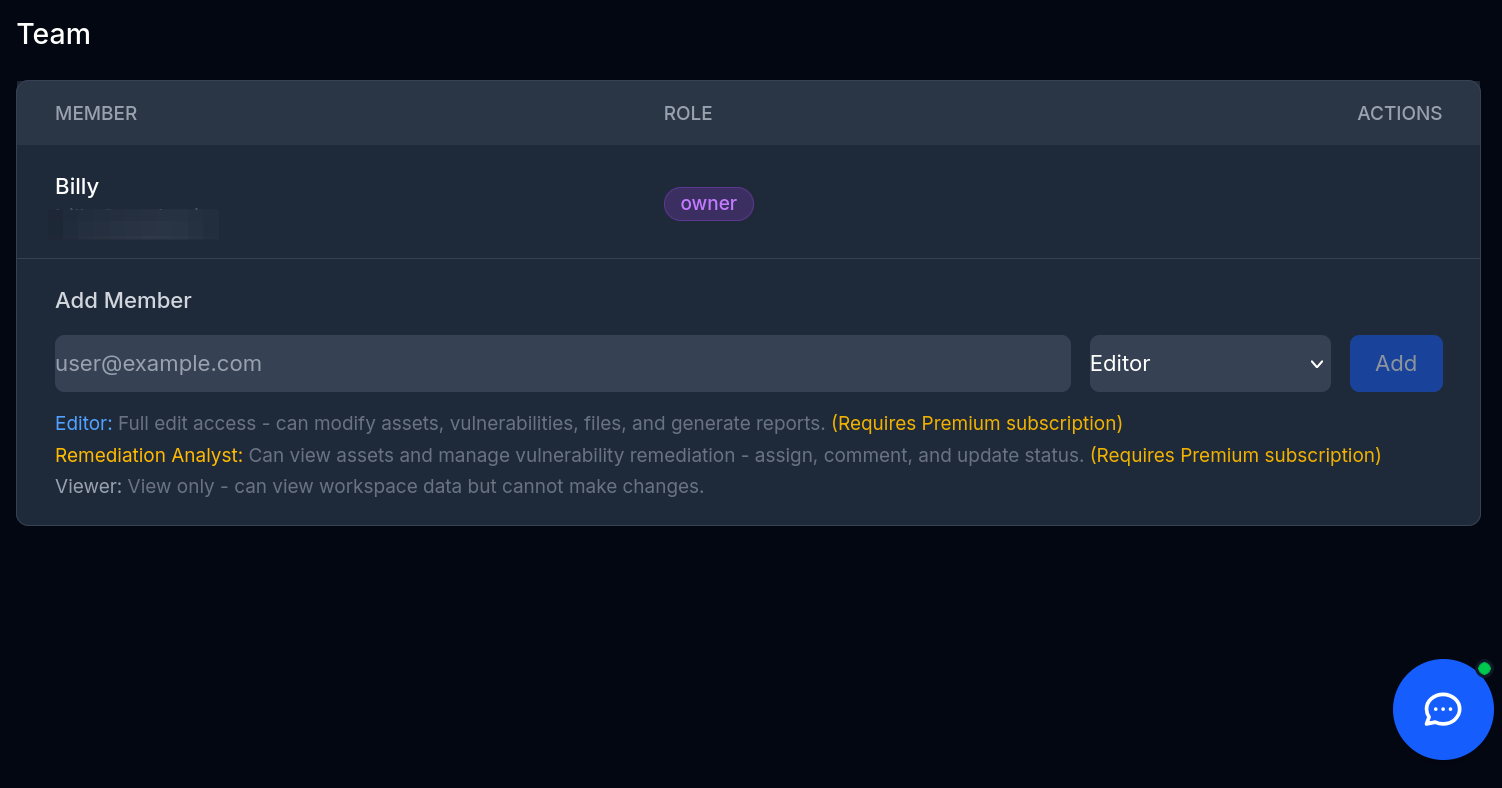
Team Collaboration
Four workspace roles, real-time WebSocket chat, remediation assignment, and a full audit trail with change tracking.
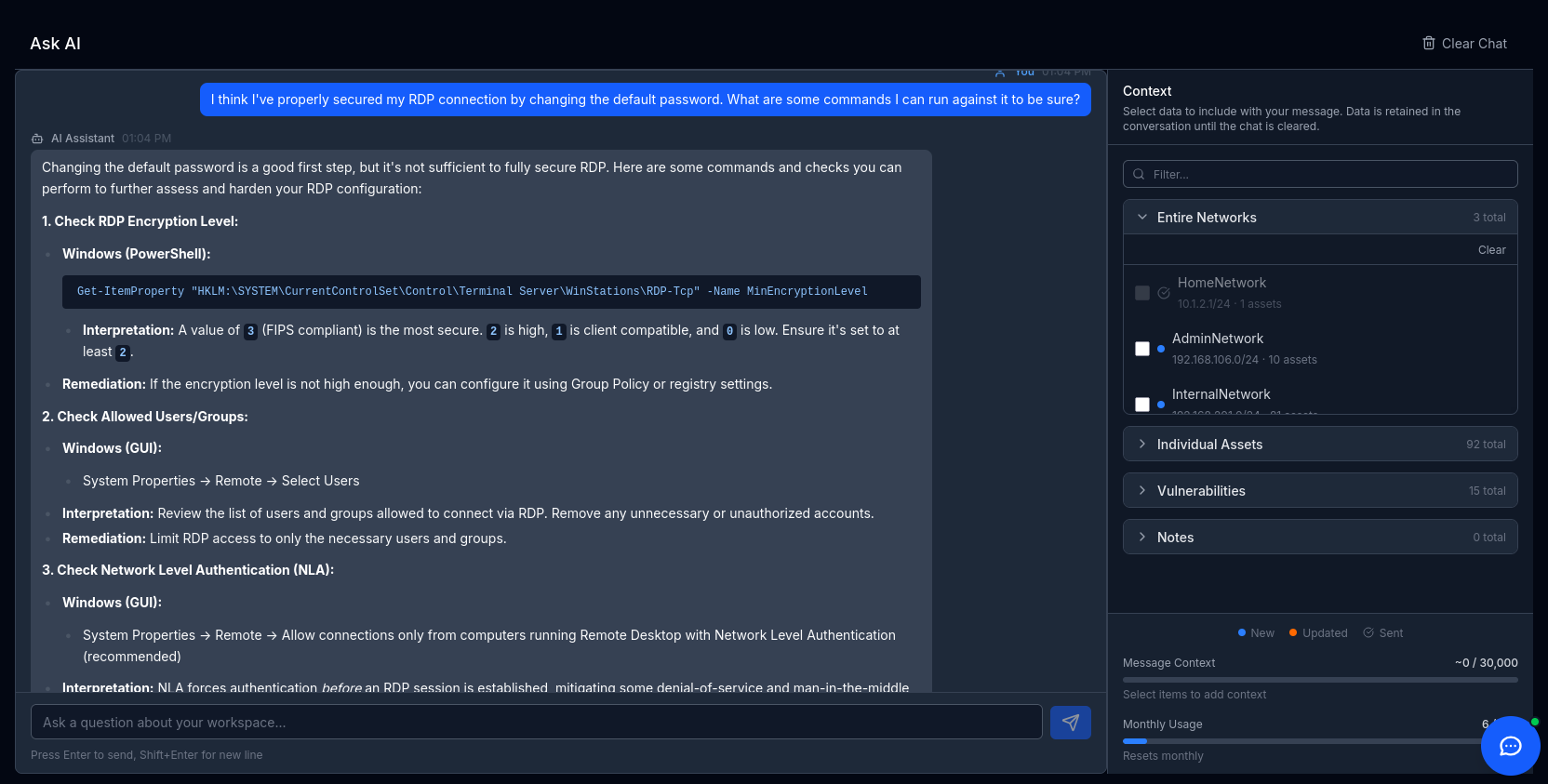
AI Security Assistant
Context-aware AI that understands your workspace data. Get remediation suggestions, vulnerability analysis, and security guidance.
Feature Deep Dives
Track Every Vulnerability From Discovery to Remediation
Manage the full vulnerability lifecycle with structured workflows that keep your team aligned and your clients informed.
- CVSS scoring with CVE and CWE mapping
- Multi-asset linking — one vulnerability, many affected hosts
- Status workflow: Identified, Validated, Remediated
- Proof and evidence attachments per vulnerability-asset pair
- Save findings to your reusable template library
- Remediation assignment with comments and timeline
Complete Attack Surface Visibility
Map every asset, network, and service in your environment with detailed classification and intelligent discovery.
- Network and CIDR scoping with VLAN support
- 15+ asset types: servers, routers, switches, IoT, and more
- Port and service discovery with protocol detection
- OS detection and MAC vendor classification
- Custom tagging system for flexible organization
- Bulk import assets from scanner results
Seven Scanner Formats. Plus Your Own Scanning Agent.
Bring results from your existing tools or run scans directly with deployable agents — Hawkra fits into any workflow.
- Parse Nmap, Nessus, OpenVAS, Burp Suite, OWASP ZAP, BloodHound, and WingSpan
- Deploy remote scanning agents with approval workflow
- Configurable scan profiles with NSE script support
- Auto-create assets, ports, and vulnerabilities from imports
- Import history with detailed result tracking
Client-Ready Reports in One Click
Generate professional penetration testing reports that impress clients and satisfy compliance requirements.
- DOCX template engine with customizable placeholders
- Repeating sections for assets and vulnerabilities
- Embedded images and proof-of-concept evidence
- Automated risk scoring and severity classification
- Export data to CSV and JSON formats
- Custom branding with logo support
Built-In Reconnaissance Without Leaving the Platform
Perform OSINT research directly within Hawkra — no tab switching, no context loss, results feed right into your workspace.
- WHOIS domain and IP lookups
- DNS record enumeration
- Shodan host intelligence integration
- Have I Been Pwned breach and paste checks
- GeoIP location mapping
- Copy results directly to clipboard for quick documentation
Automate Compliance Assessments
Map your security posture against industry frameworks with intelligent auto-population and gap analysis.
- NIST CSF 2.0, ISO 27001, CIS Benchmarks, and CMMC Level 1, 2, and 3 built in
- Auto-populate control responses from scan and asset data
- Gap analysis with visual progress metrics
- Evidence management per control
- Encrypted compliance notes for sensitive responses
- Export compliance reports for auditors
Built for Security Teams, AND Solo Operators
Hawkra scales with you — from solo consultants to enterprise security operations with full role-based access control.
- Four workspace roles: Owner, Editor, Analyst, Viewer
- Real-time WebSocket team chat per workspace
- Remediation assignment and progress tracking
- Full audit trail with old and new value tracking
- Email invitations with role assignment
- Workspace-scoped data isolation
An AI That Understands Your Security Context
Not a generic chatbot. Hawkra's AI assistant has full access to your workspace data for actionable security guidance, and TalonStrike takes it a step further by autonomously running penetration tests against your targets from inside an isolated container.
- Workspace-aware conversations with full vulnerability context
- AI-driven remediation guidance and prioritization
- TalonStrike autonomous red teaming with live terminal streaming
- Findings logged directly into your workspace as they're discovered
- Cloud (Gemini) or local LLM support for air-gapped environments
- Optional per-asset and per-vulnerability context — you choose what data is sent
Self-Hosted Deployment
Deploy On Your Infrastructure. Keep Your Data.
Run Hawkra entirely in your environment with active scanning capabilities, offline operation, and air-gapped network support. Your vulnerability data never leaves your perimeter.
Active WingSpan Scanning
Run authenticated scans directly from your network perimeter
Air-Gap Compatible
Full functionality without internet connectivity
Full Data Sovereignty
Your infrastructure, your data, your control
Optional Encrypted S3 Storage
Store files in Amazon S3 with encryption — your data stays where you want it
Optional AI LLM Support
Connect a cloud or local LLM on your terms — AI features are entirely opt-in
Set Your Limits
We don't limit what you do on your own hardware — no artificial caps or restrictions
Frequently Asked Questions
Ready to Streamline Your Security Assessments?
Start with our free tier — no credit card required.