Vulnerability ManagementPenetration TestingCompliance
One Platform.
Streamline your security assessments with AI-powered intelligence, real-time collaboration, and professional reporting — all in one encrypted workspace.
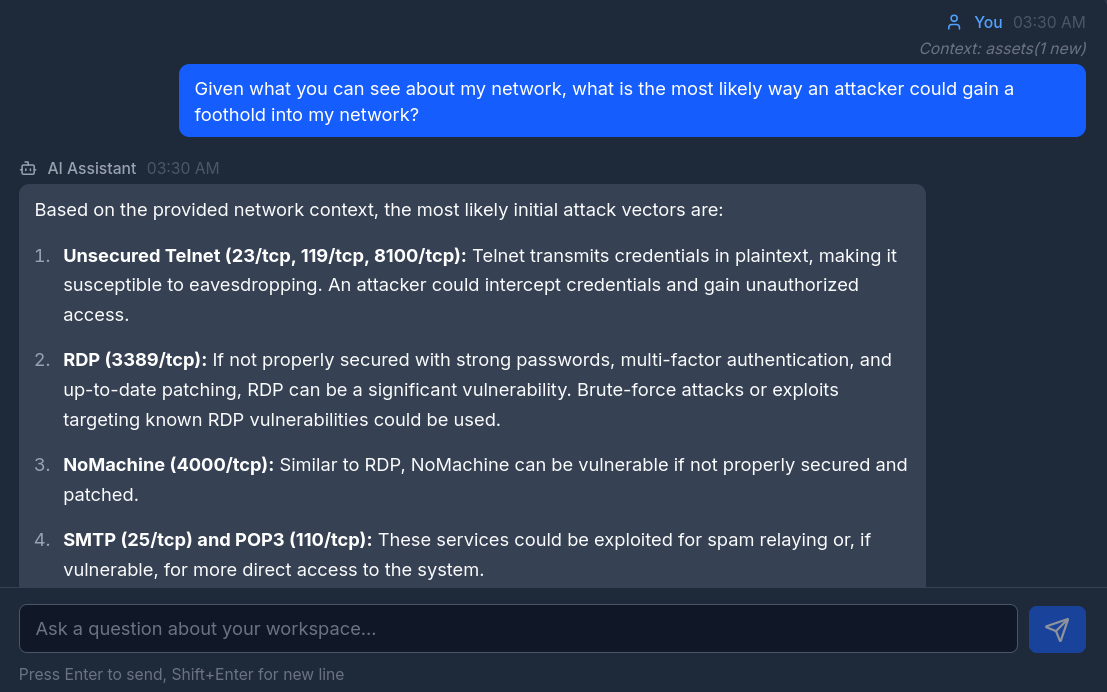
AI-Powered Security Intelligence
Ask questions about your workspace data, get remediation suggestions, and accelerate report writing with a context-aware AI assistant that understands your entire security posture. Or let TalonStrike do the heavy lifting: point it at a target and watch it run a full penetration test on its own, streaming results to your terminal in real time and logging findings as it goes.
- Context-aware analysis of your vulnerability data
- Intelligent remediation guidance and prioritization
- Accelerated report writing and finding descriptions
- Autonomous AI red teaming with real-time terminal streaming
Everything You Need for Security Assessments
A complete toolkit for vulnerability management, penetration testing, and compliance auditing.
Vulnerability Tracking
Track vulnerabilities with CVSS scoring, CVE/CWE mapping, multi-status workflows, and asset linking across your entire infrastructure.
Asset Discovery & Inventory
Catalog hosts, services, and ports with 15+ device types, OS detection, MAC vendor classification, and custom tags.
Encrypted Credential Vault
Store domain, service, database, and API credentials with AES-256-GCM envelope encryption and per-workspace keys.
Professional Report Generation
Generate client-ready DOCX reports with customizable templates, risk scoring, evidence attachments, and remediation guidance.
Real-time Team Collaboration
Work together with WebSocket-powered chat, role-based access control, audit logging, and shared workspaces.
Customizable Dashboard
Build your view with drag-and-drop widgets showing vulnerability stats, severity breakdowns, remediation progress, and more.
See Your Entire Security Posture at a Glance
One dashboard for assets, vulnerabilities, compliance, and remediation tracking.

Import From the Tools You Already Use
Auto-populate assets, ports, and vulnerabilities from industry-standard scanner formats.
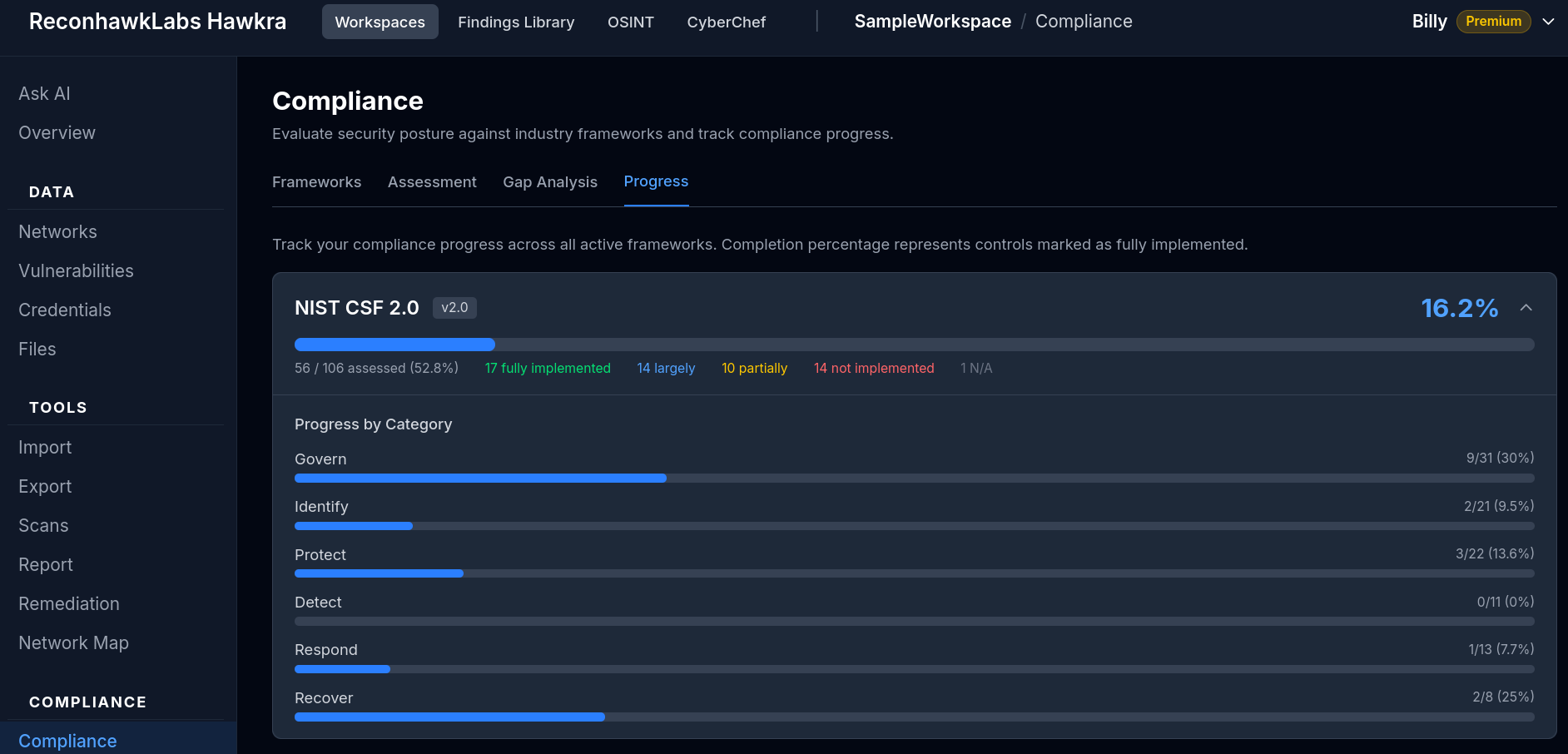
Built-In Compliance Auditing
Assess your security posture against industry frameworks. Auto-populate controls from your assessment data, track evidence, and run gap analysis — all without leaving the platform.
- Auto-populate from assessment data
- Evidence management per control
- Gap analysis with progress tracking
- Export compliance reports
How It Works
Get started in minutes, not days.
Create a Workspace
Set up your project scope, define networks, and invite team members with role-based permissions.
Import & Discover
Import scan results from 7+ formats, add assets manually, or run active scans with WingSpan, our scanning Agent.
Analyze & Report
Track findings across your infrastructure and generate professional reports for your clients.
Remediate & Mitigate
Assign vulnerabilities to team members, track remediation progress, and verify corrections with proof attachments.
Validate
Use TalonStrike to automatically launch a penetration test against your targets, confirm that fixes hold up, and make sure the asset is actually secure before closing the book.
Deploy Your Way
Choose the deployment model that fits your security requirements.
Cloud (SaaS)
Managed hosting with zero setup
- Free tier available — no credit card required
- Automatic updates and maintenance
- Stripe-powered billing and usage tracking
- No infrastructure to manage
Self-Hosted
Full control on your infrastructure
- Active scanning capabilities with Nmap
- Air-gapped and offline network support
- NDA-compliant deployment options
- All premium features included